In this article, we have gathered the basic functions related to the Webmail.ee environment that will make it easier for you to use the application.
Two- and three-panel view
You can choose which mailbox view you prefer. To do this, in the menu Settings -> General , you can choose the distribution of the panes under Screen view.
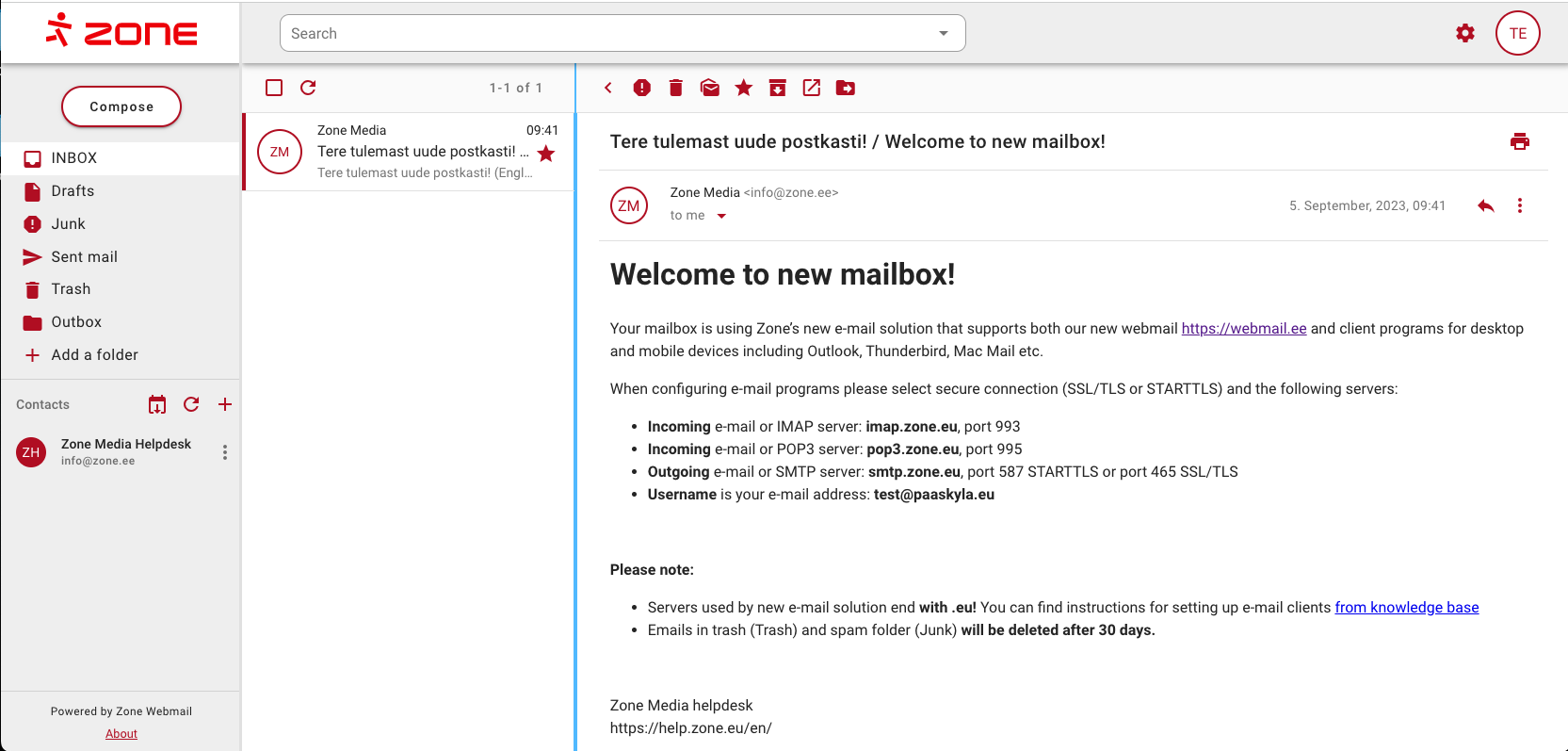
By default, the mailbox is displayed with three panels, i.e. a list of folders, a list of emails and the contents of the email:
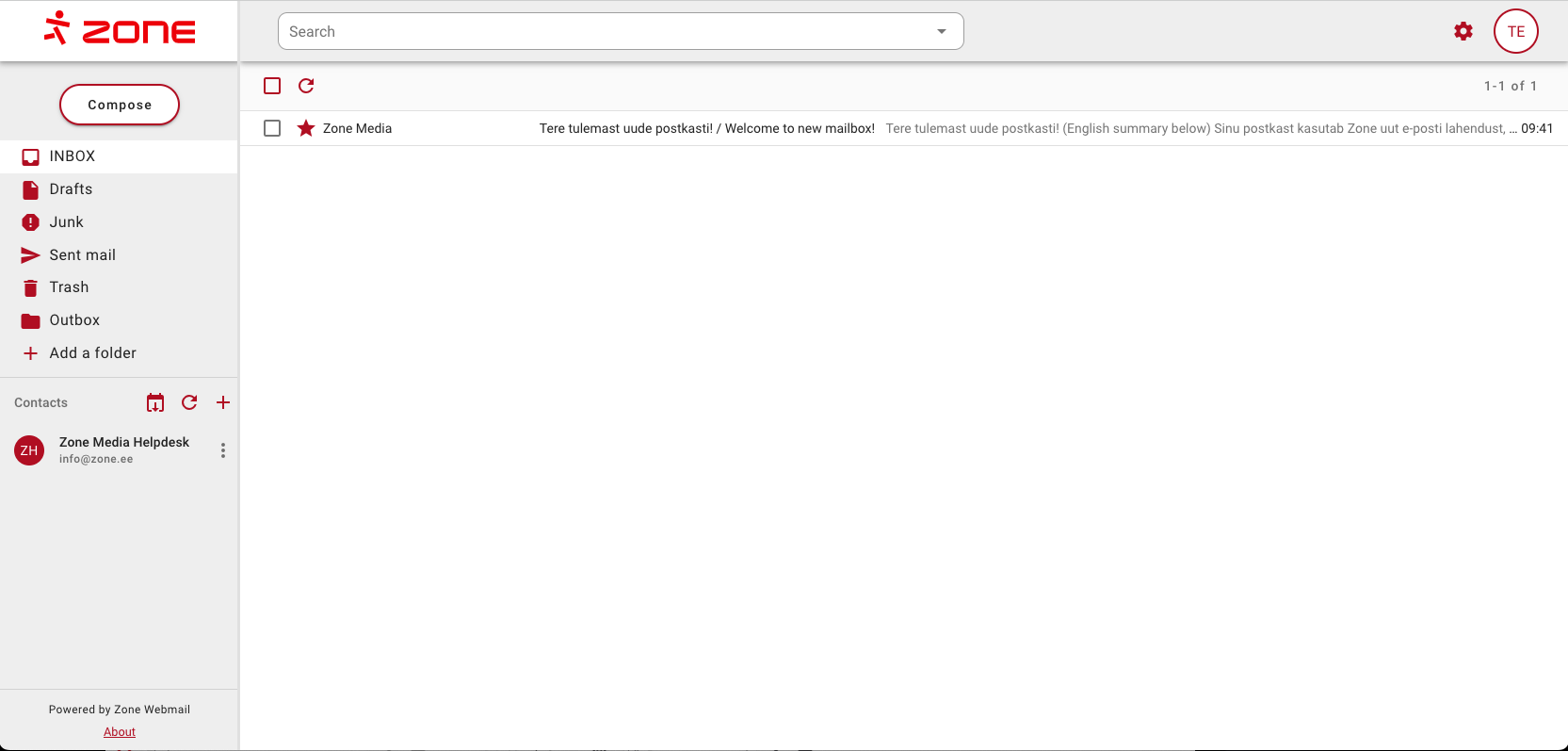
In the two-pane view, only the list of folders and the list of emails are displayed. Clicking on an email opens it in a second pane:
Import contacts
Webmail.ee supports importing contacts in CSV format from external applications such as Gmail, Outlook and Mac Mail etc. If CSV file properly formatted, it does not directly matter where the contacts are exported from.
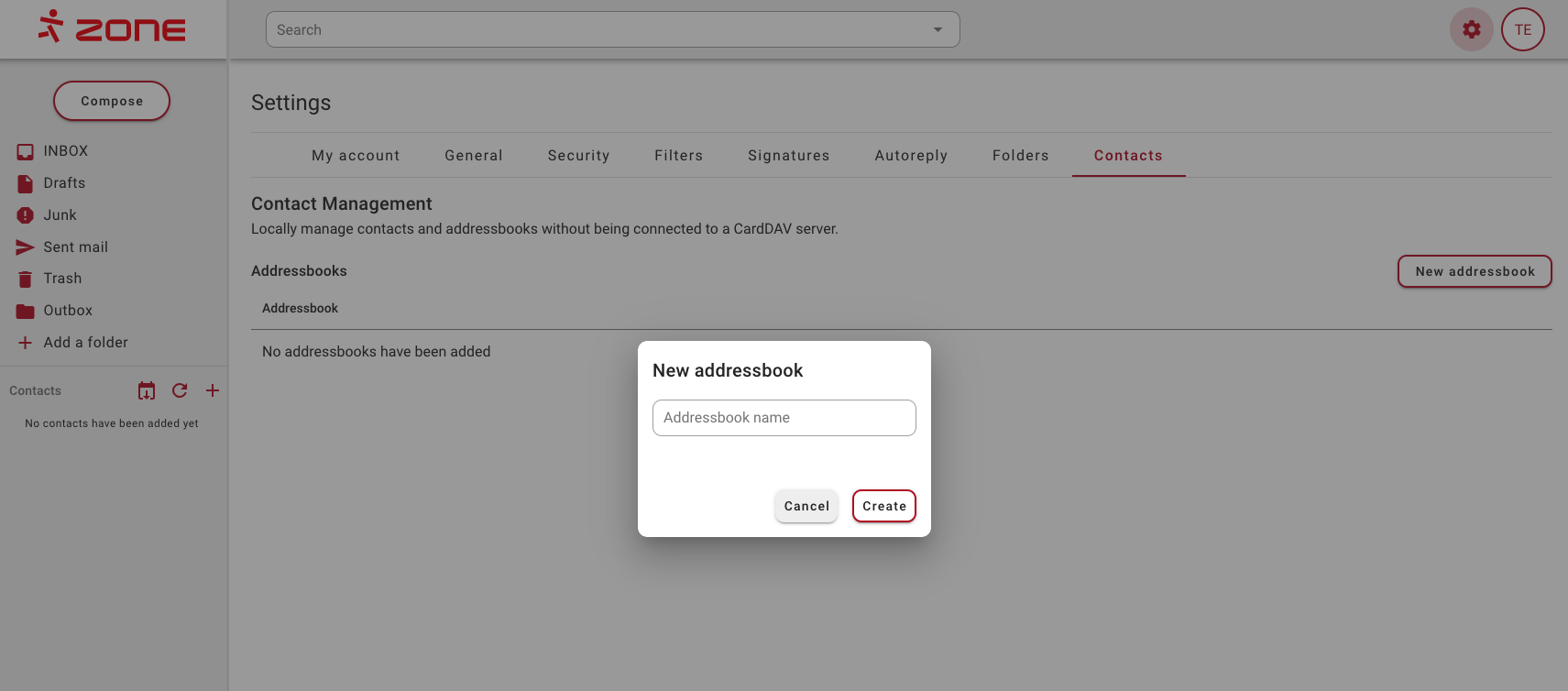
You can then import the downloaded file into your Webmail.ee. If you don’t have an address book there, add one from the menu Settings ->Contacts -> New addressbook.
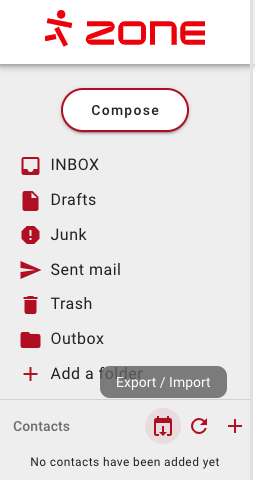
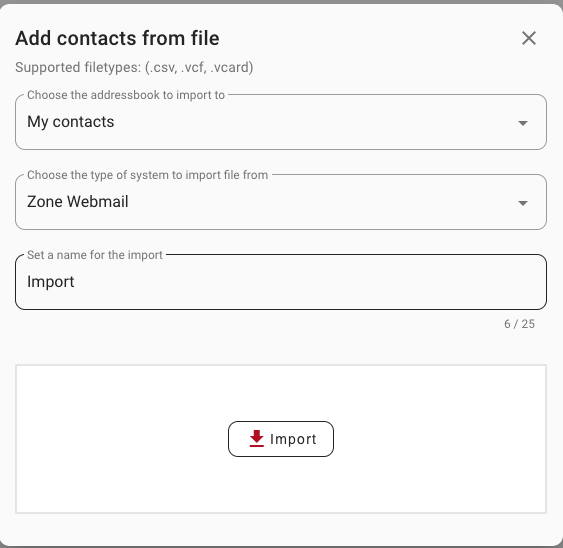
Now in the Contacts section of the left menu, you can choose Export/Import -> Import
In the new window, you can import a contact file by dragging and dropping it in your browser into the window Import
When the correct file is imported, the contacts are automatically added to the contact list.
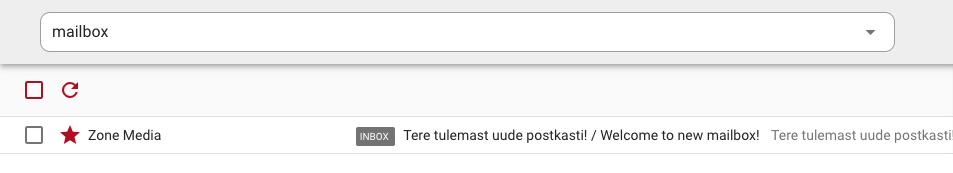
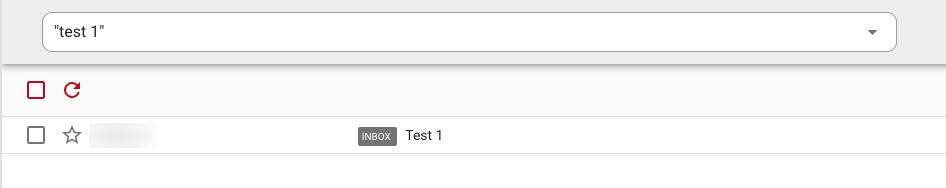
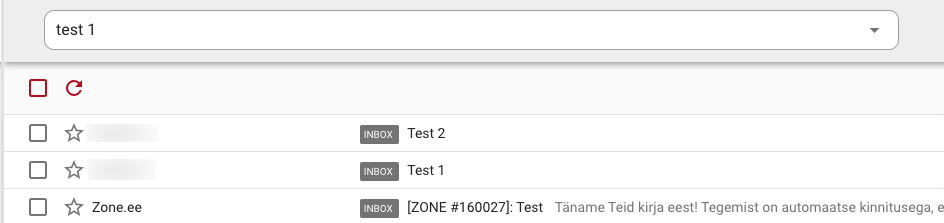
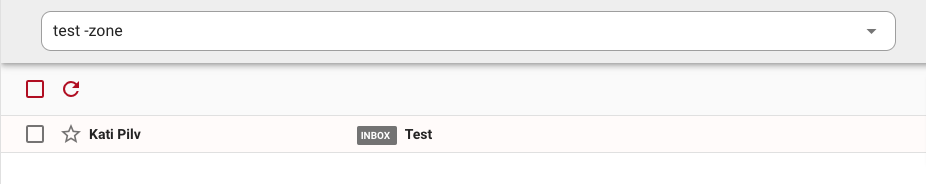
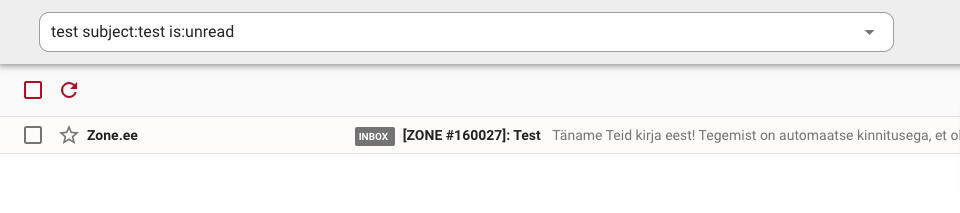
Email search
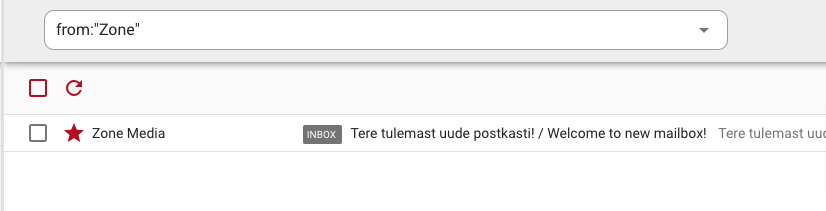
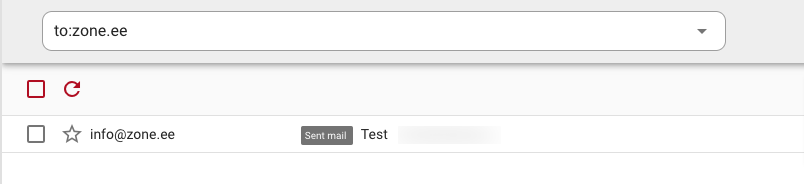
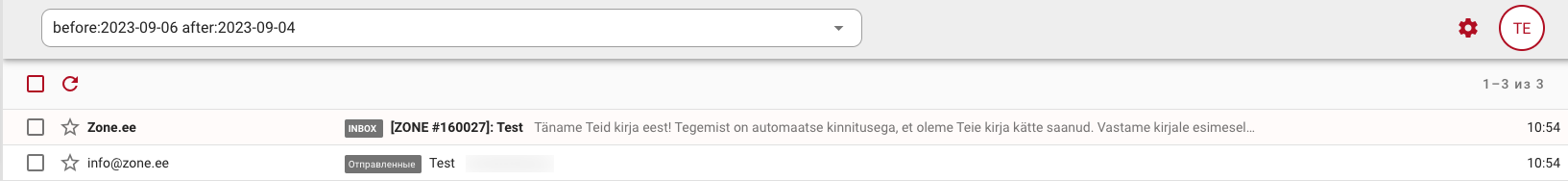
Webmail.ee uses the FULLTEXT index to search for text. More detailed search parameters are given in the table below (click on the arrow to see examples!)Otsinguparameetrid
| Search option | Search кeyword |
|---|---|
| Sender | |
| Recipient |
|
| Subject |
|
| Date/period |
|
| Starred | is:starred |
| Read | is:read |
| Unread | is:unread |
| Emails with an attachment |
|
| Email size |
|
| Specific folder |
|
| Exact word | |
| Exact phrase | |
| Remove word from results | |
| Combined search |
Filtering emails
Webmail.ee allows you to configure server-level email filters.
Server-level filtering means that emails are filtered before they even reach your mailbox. For example, you can move emails to different folders based on keywords, and this will happen automatically in all email applications that you use with the same email address.
Filters are only applied to new incoming messages and are not applied to existing emails.
You can apply multiple filters to the same email at the same time. The exception is deleting an e-mail. If a filter deletes an email, no filters other than forwarding the email will be applied.
Filters are applied in the order in which they are listed in the settings. If one filter already specifies an action, the other filter will not overwrite it. For example, if one filter performs the action of moving email to folder X, the second filter will not move the email to folder Y. The exception is marking as spam/not spam.
See the next article for more examples on filtering emails.
Security, two-factor authentication, application password, etc.
Security is seen as one of the most important foundations for the development of the Webmail.ee environment and can be ensured by the user in the following ways.
Two-factor authentication (2FA)
You can set up two-factor authentication for an email account. This means that the account cannot be logged in with just a password, but requires a second factor as well. See the following article for a more detailed configuration instructions.
Application password
If you want to use two-factor authentication and, for example, an email application (Outlook, Mac mail, etc.) at the same time, you need to set the application password for the account.
The application password is an automatically generated secure password that can only be used for authentication on mailboxes that use secure IMAP and SMTP connections.
Detailed instructions on how to activate the application password can be found here.
Authentication with a U2F-compliant physical security key.
In addition to the classic TOTP authentication tool, Webmail also supports the WebAuthn standard. This means that logging in is also possible, e.g. by fingerprint from a smart device, FaceID, Windows Hello or a security key (Yubikey, etc.).
You can read more about this in our blog article.
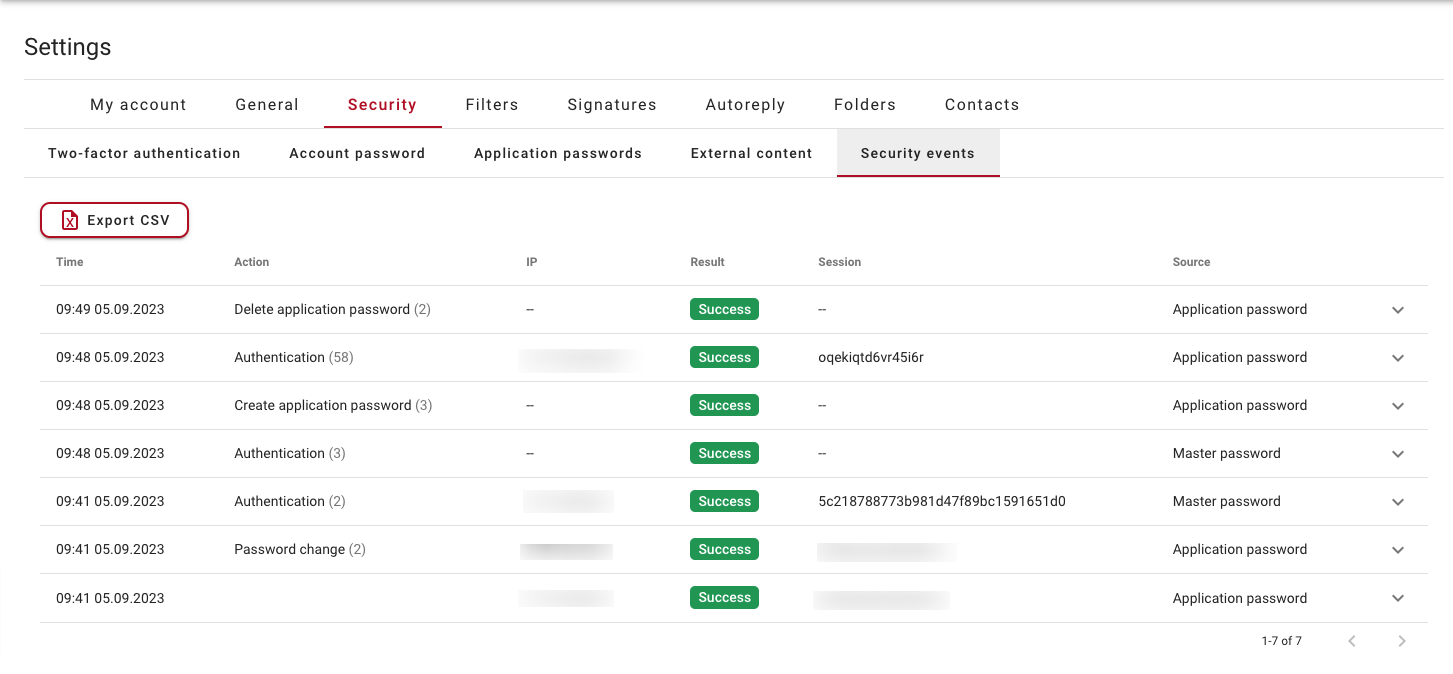
Security events
If necessary, the user can check where and how the authentication (or authentication attempt) of his mailbox was made. To do this, go to the Security -> Security events in the settings section.
If you have any doubts, you can easily view all login attempts. If necessary, the security events can be downloaded and transferred, for example, to your IT administrator.